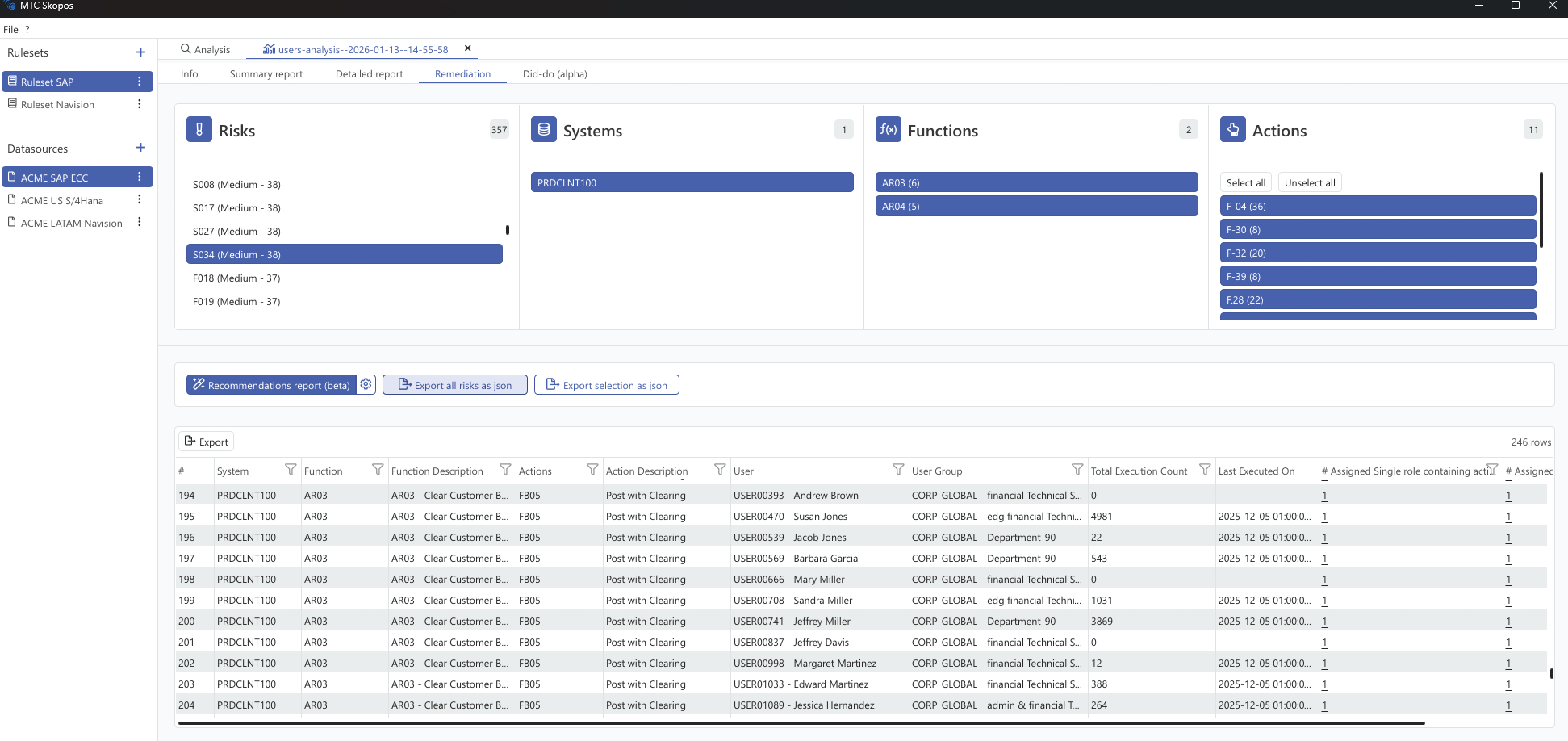
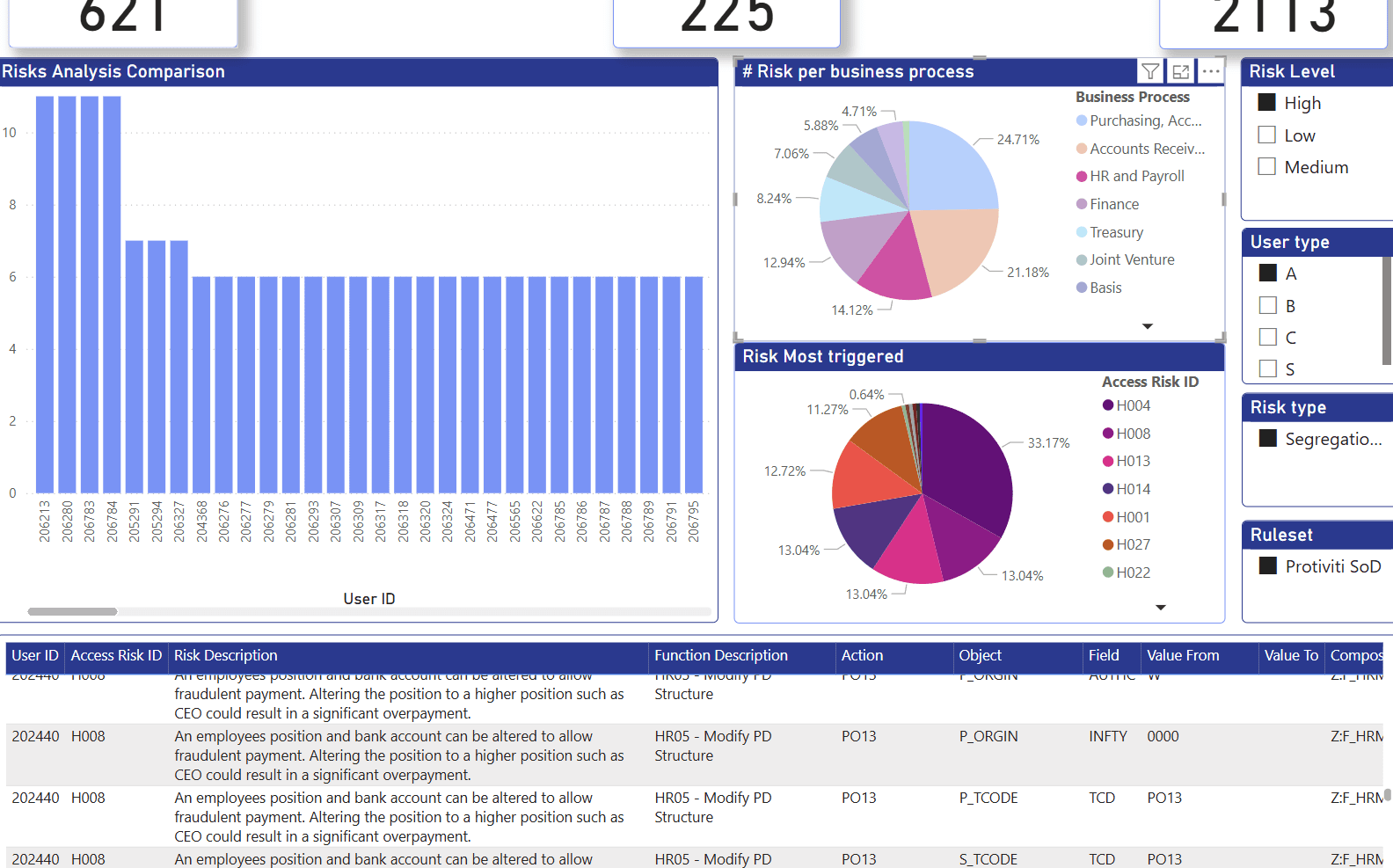
Role redesign projects typically stretch across months of consultant workshops, spreadsheet gymnastics, and back-and-forth validation cycles. The AI Role Designer collapses this into an iterative conversation: provide a functional blueprint, let AI analyze historical usage, generate a new role concept, run risk analysis, and refine until clean. Then build the roles, whether manually or through AI connected directly to SAP.
Blog Posts
Features
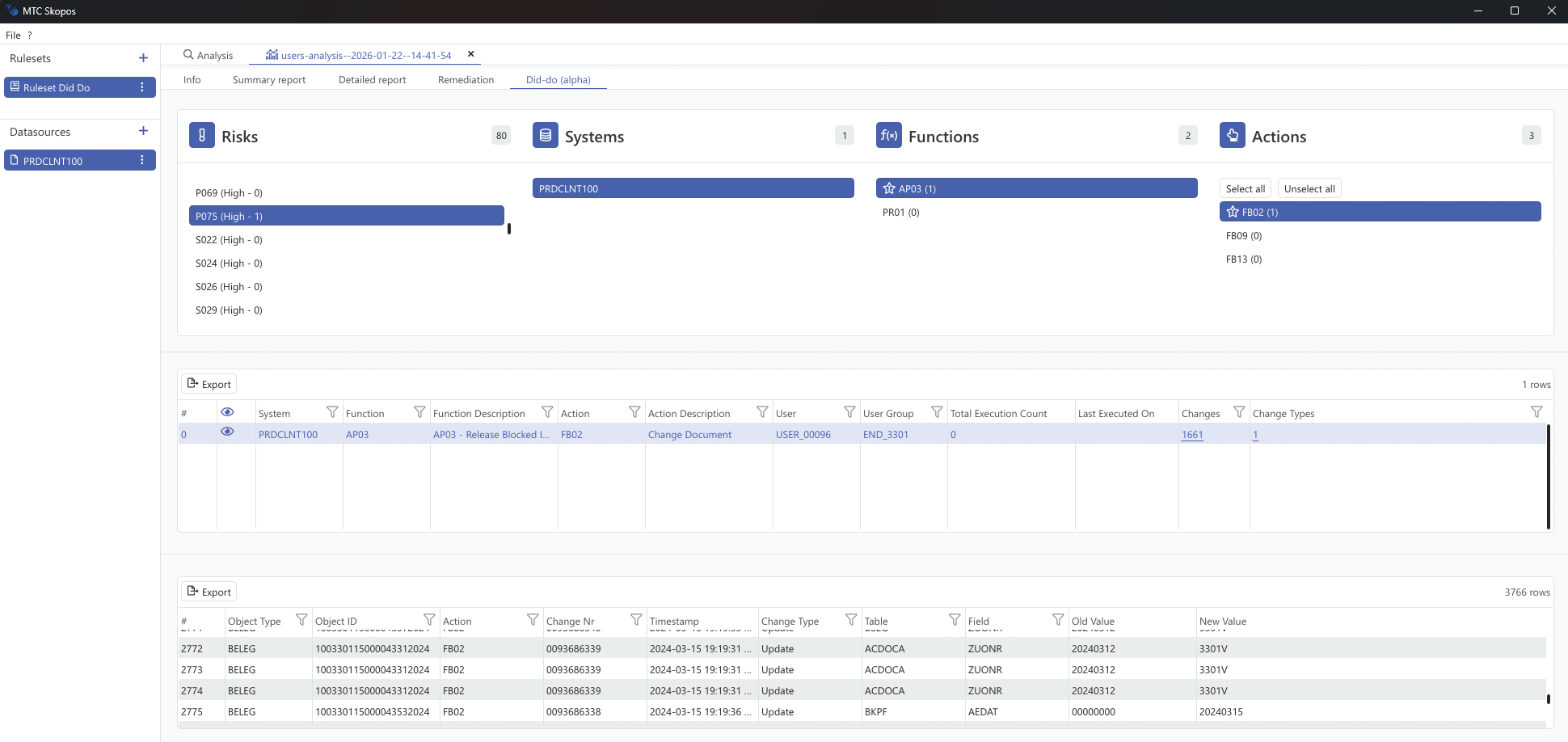
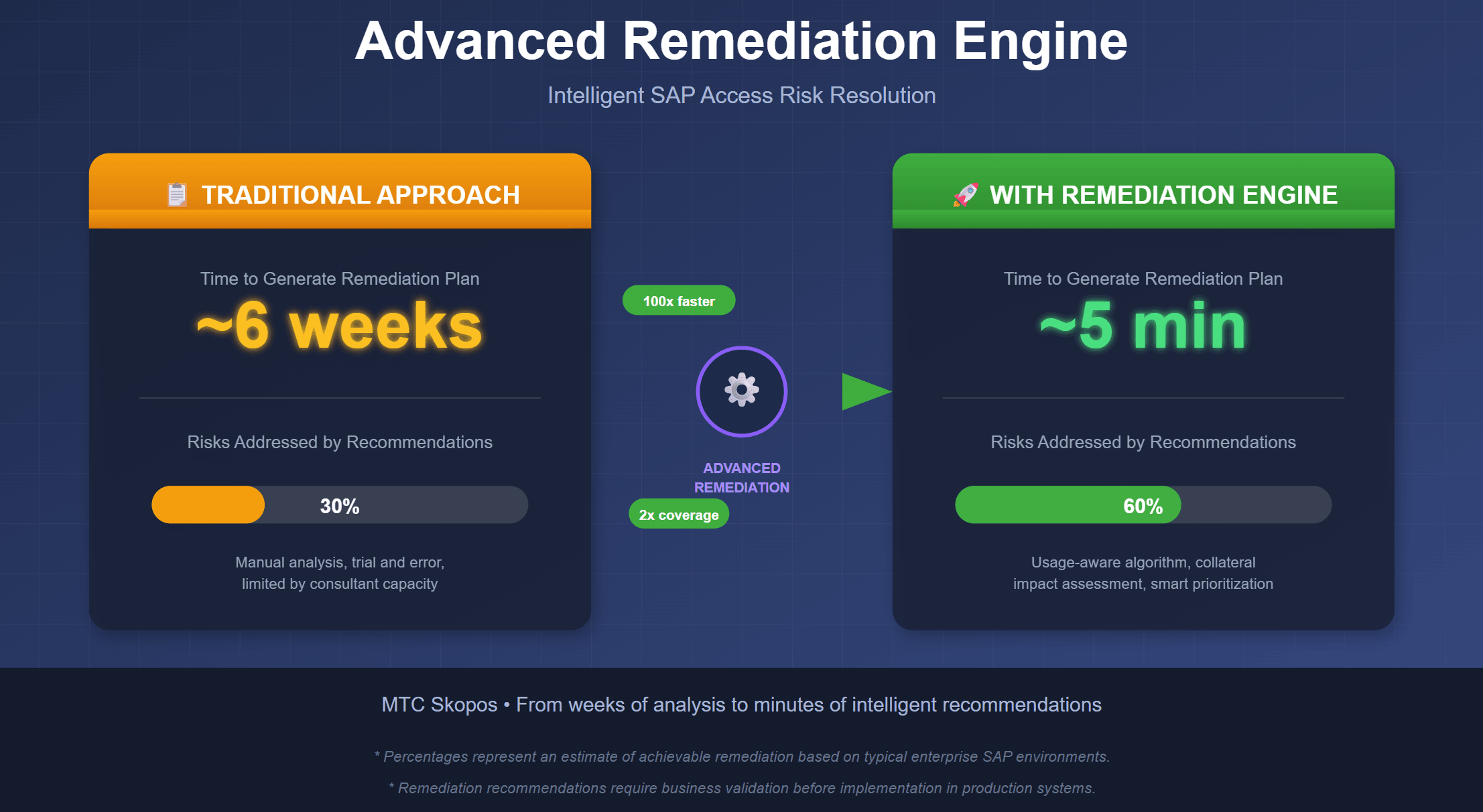
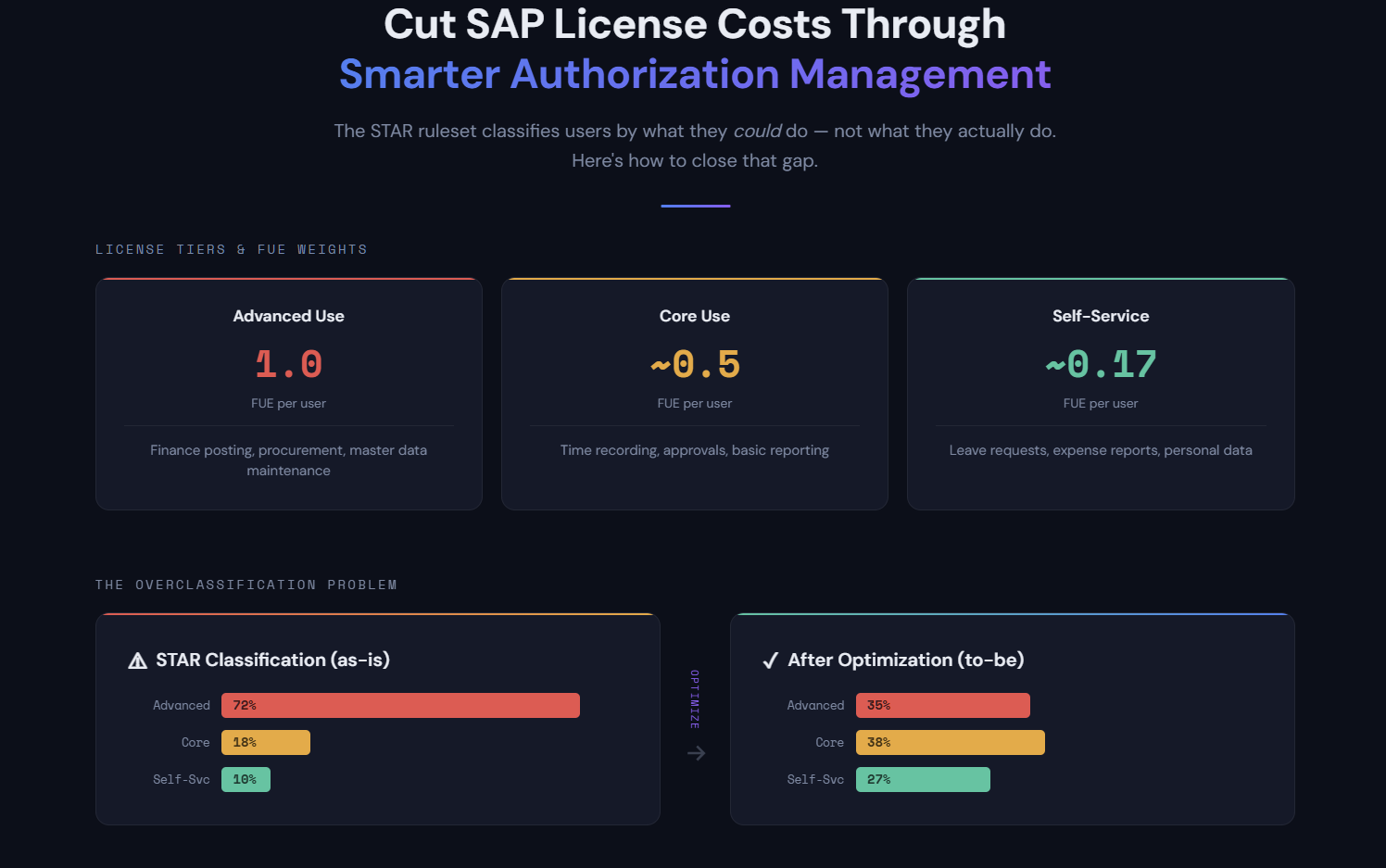
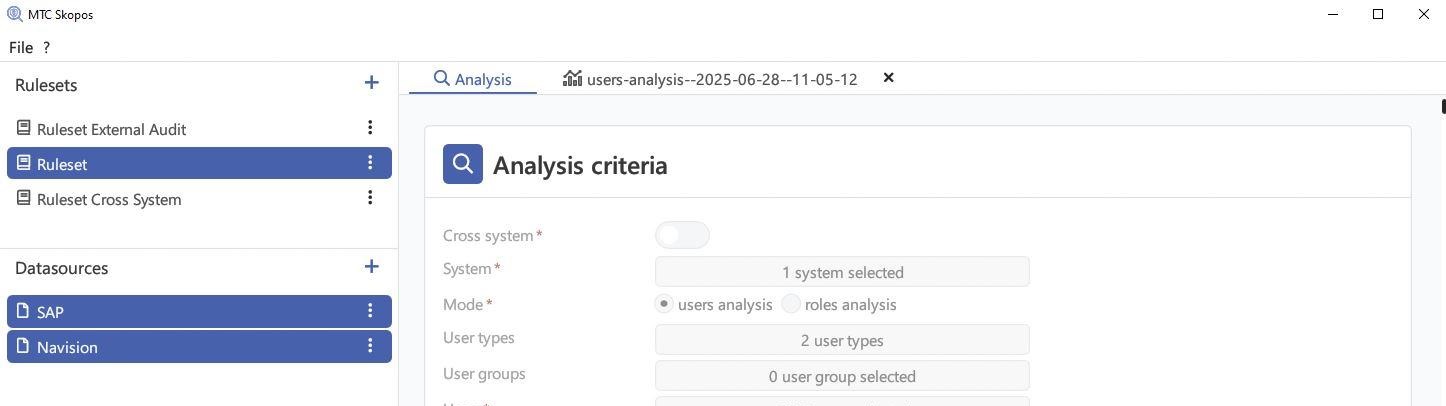
Deep dives into MTC Skopos product features: automated remediation, AI Role Designer, did-do analysis, FUE optimization, and more.
MTC Skopos
About the MTC Skopos product: positioning, case studies, and how it fits into your access risk analysis workflow.
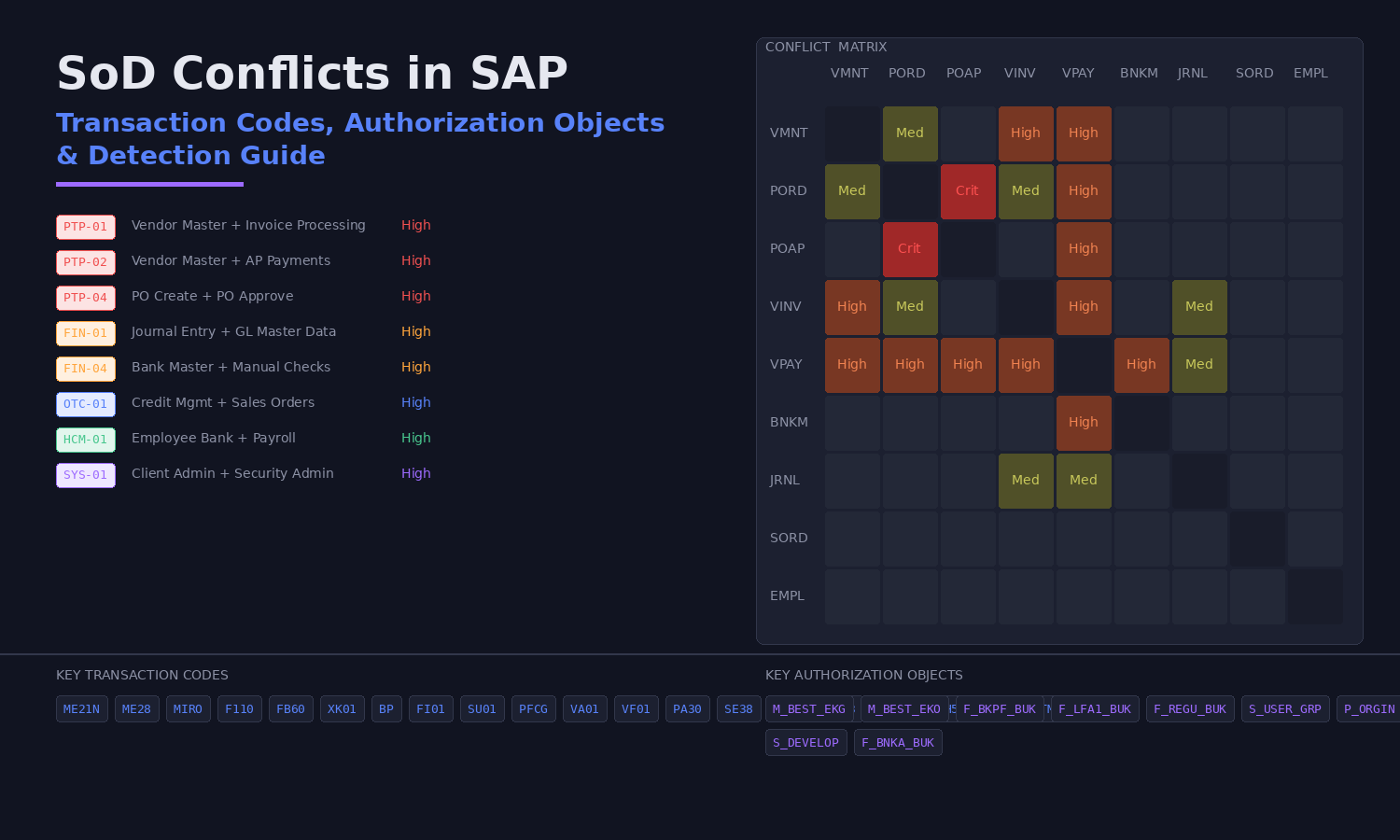
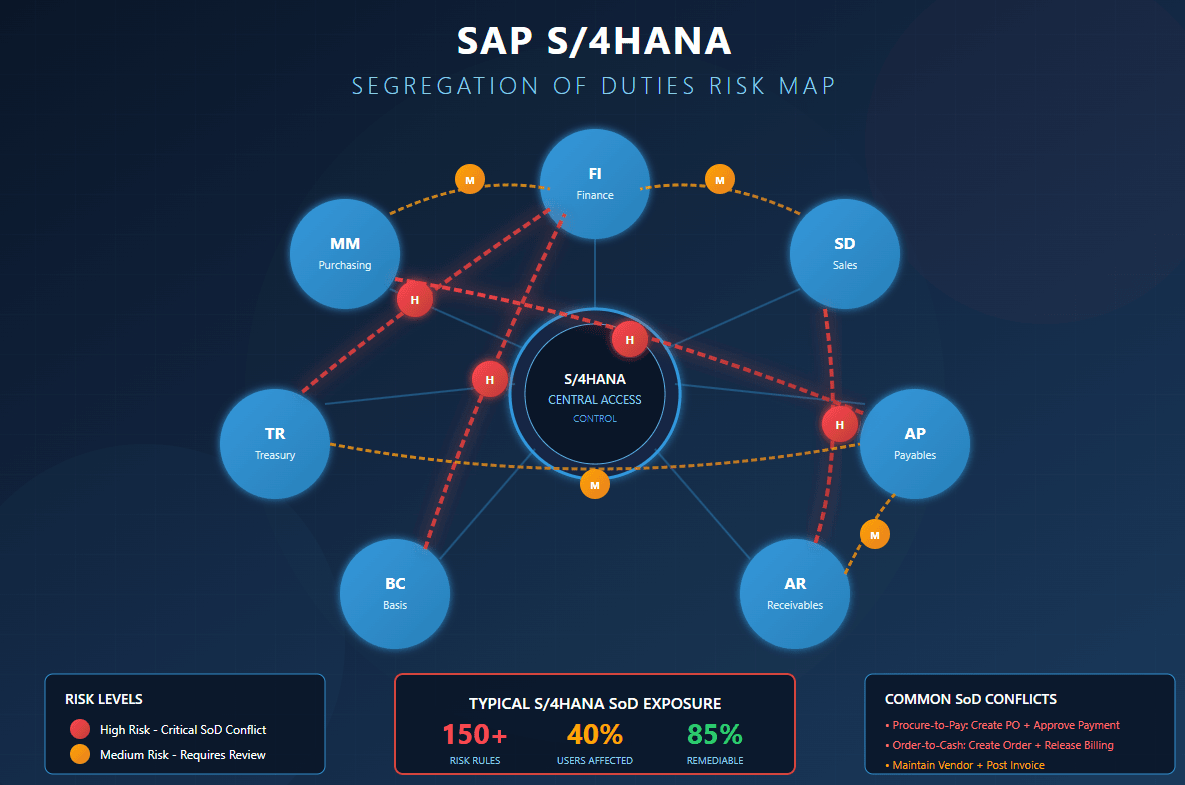
SAP Authorization
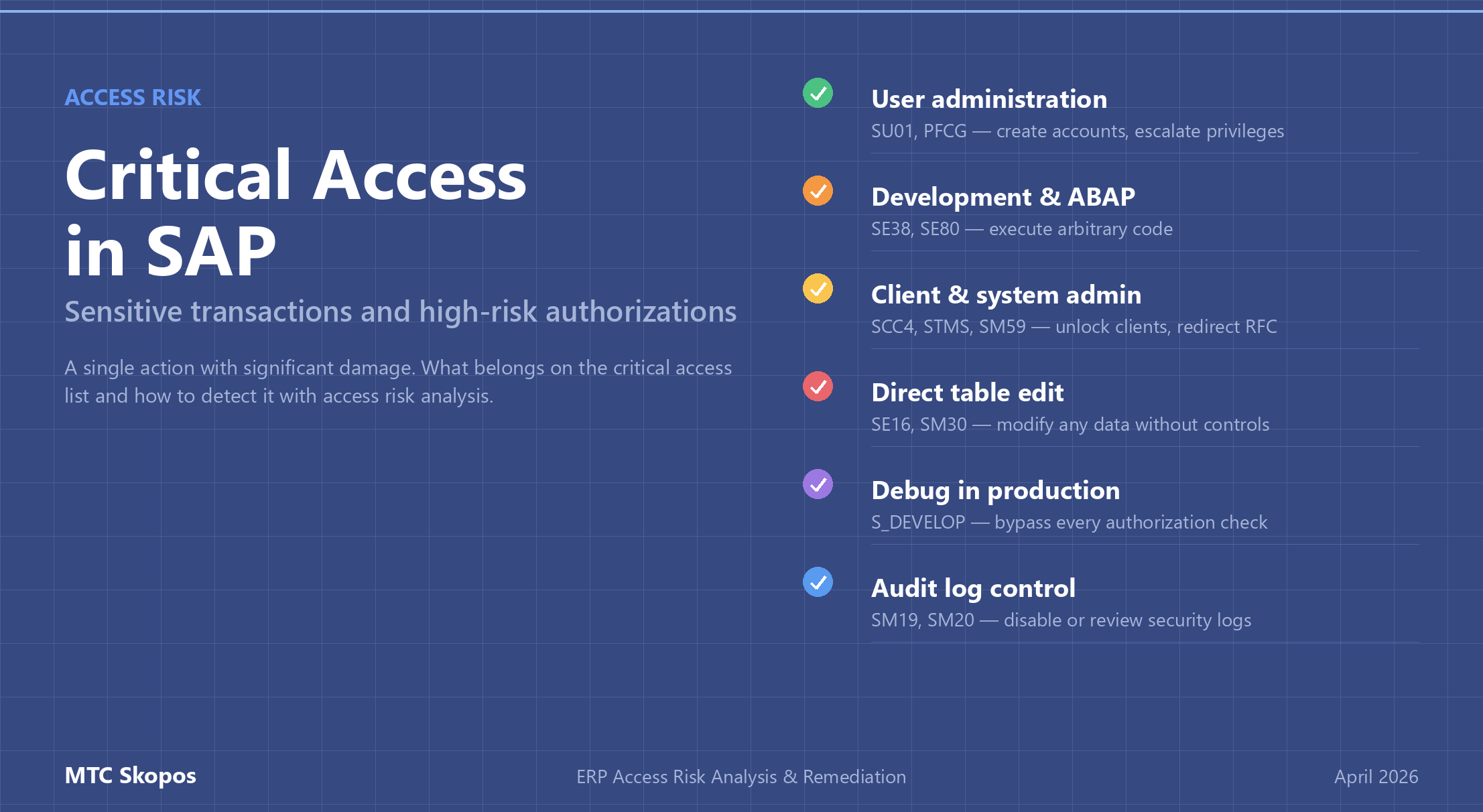
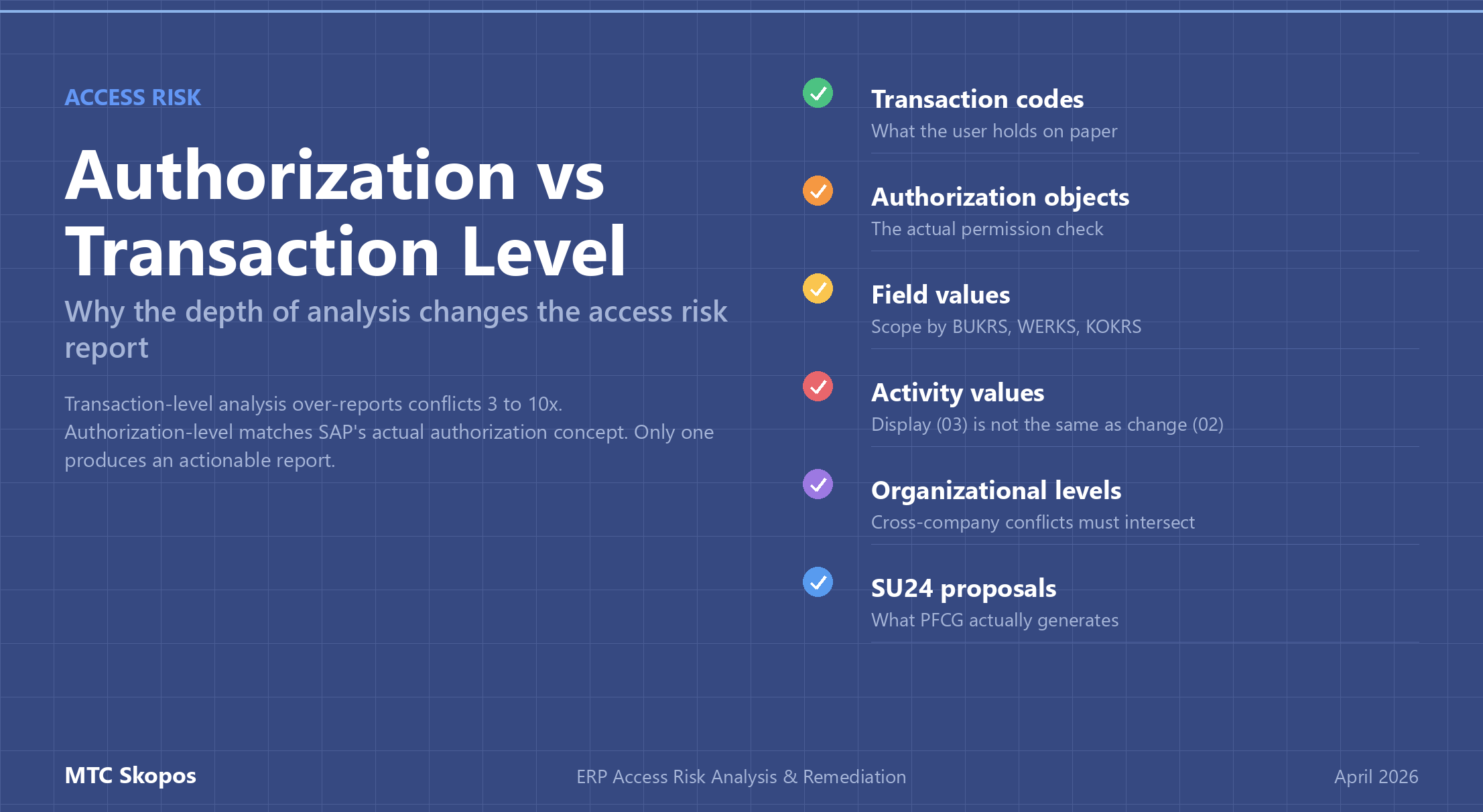
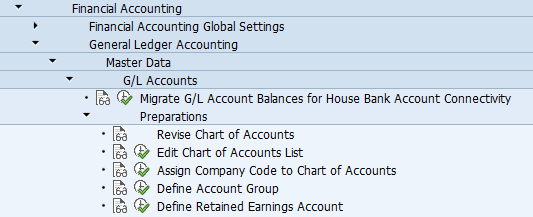
Technical SAP authorization topics: role design, critical access, SoD rulesets, S/4HANA specifics, and authorization best practices.
2026-04-06
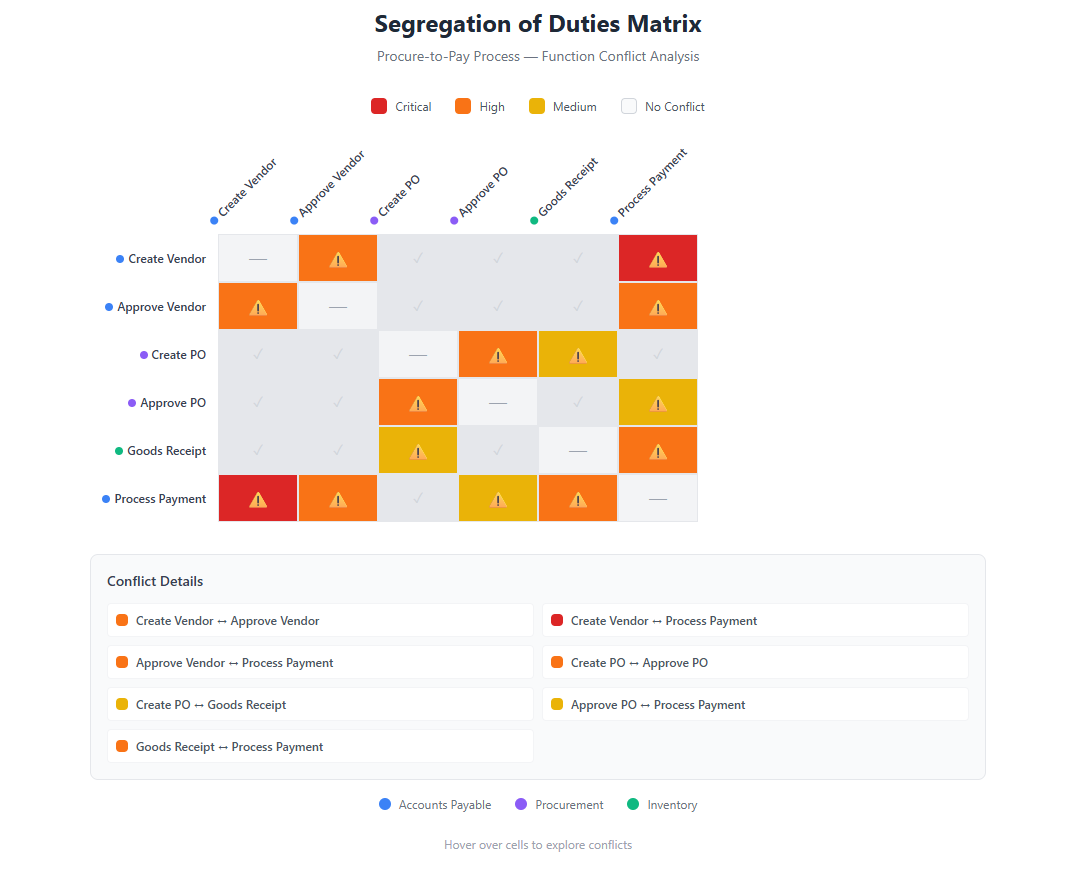
Risk and Compliance
IT audit, internal controls, and compliance fundamentals: Segregation of Duties concepts, matrices, and templates.
Perspectives
Industry perspectives and opinion pieces on AI, SaaS, data ownership, and the evolving GRC landscape.
2025-11-28