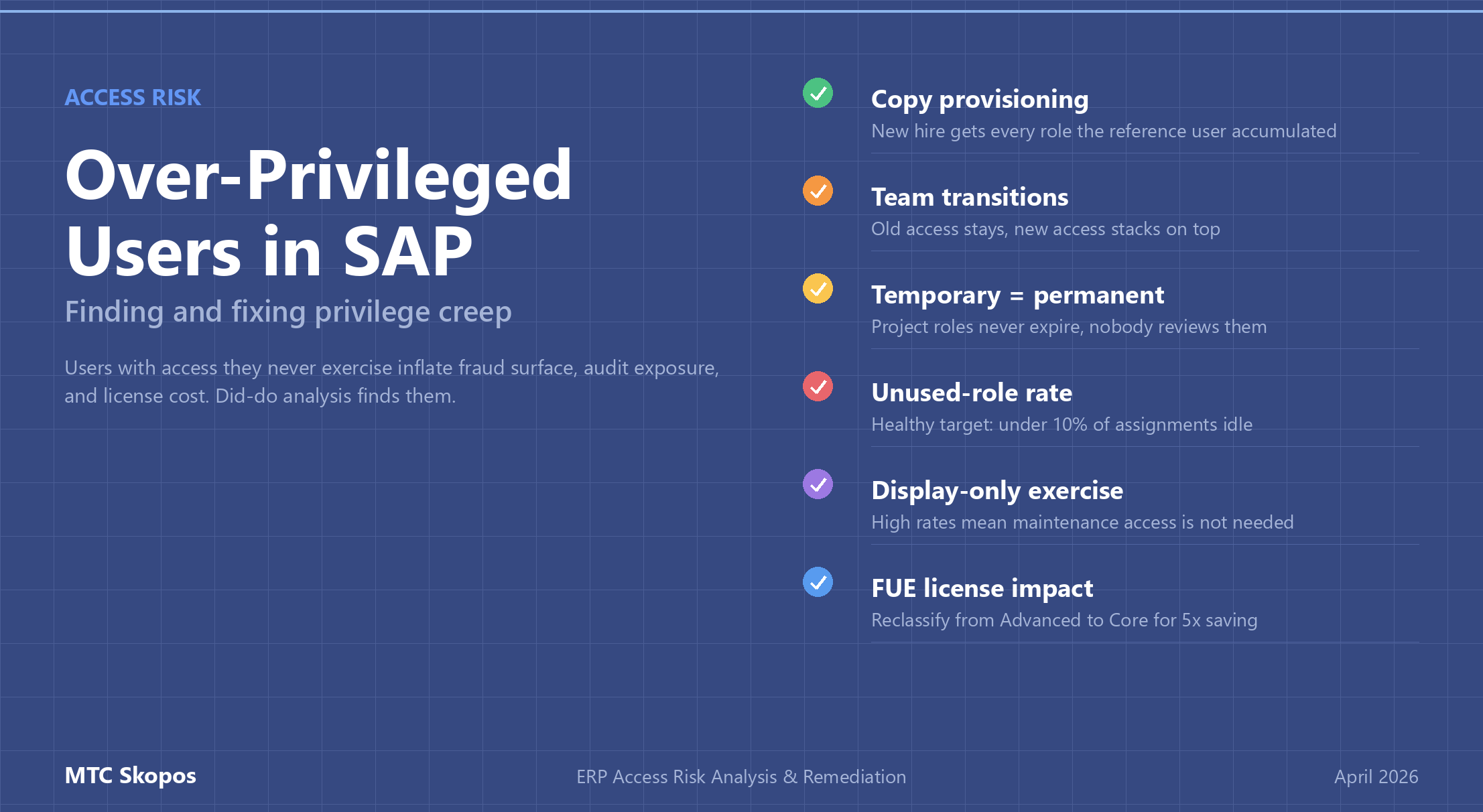
Over-privileged users are the quiet third category of access risk, behind SoD and critical access. They hold authorizations that expand their fraud surface, inflate FUE licensing, and create audit findings, even though nothing about their daily work requires the access. This guide explains how privilege creep happens, how to detect it with access risk analysis, and how to remediate without breaking business operations.
Over-privileged-users: Articles & Insights
Browse our collection of articles, tutorials, and case studies related to over-privileged-users. These resources from the MTC Skopos team provide insights on ERP security, access risk analysis, and compliance best practices.
Found 1 article on this topic.
All Articles Tagged "Over-privileged-users"
Want to learn more about ERP access risk management? Explore MTC Skopos features for comprehensive Segregation of Duties analysis and remediation.
MTC Skopos © 2026