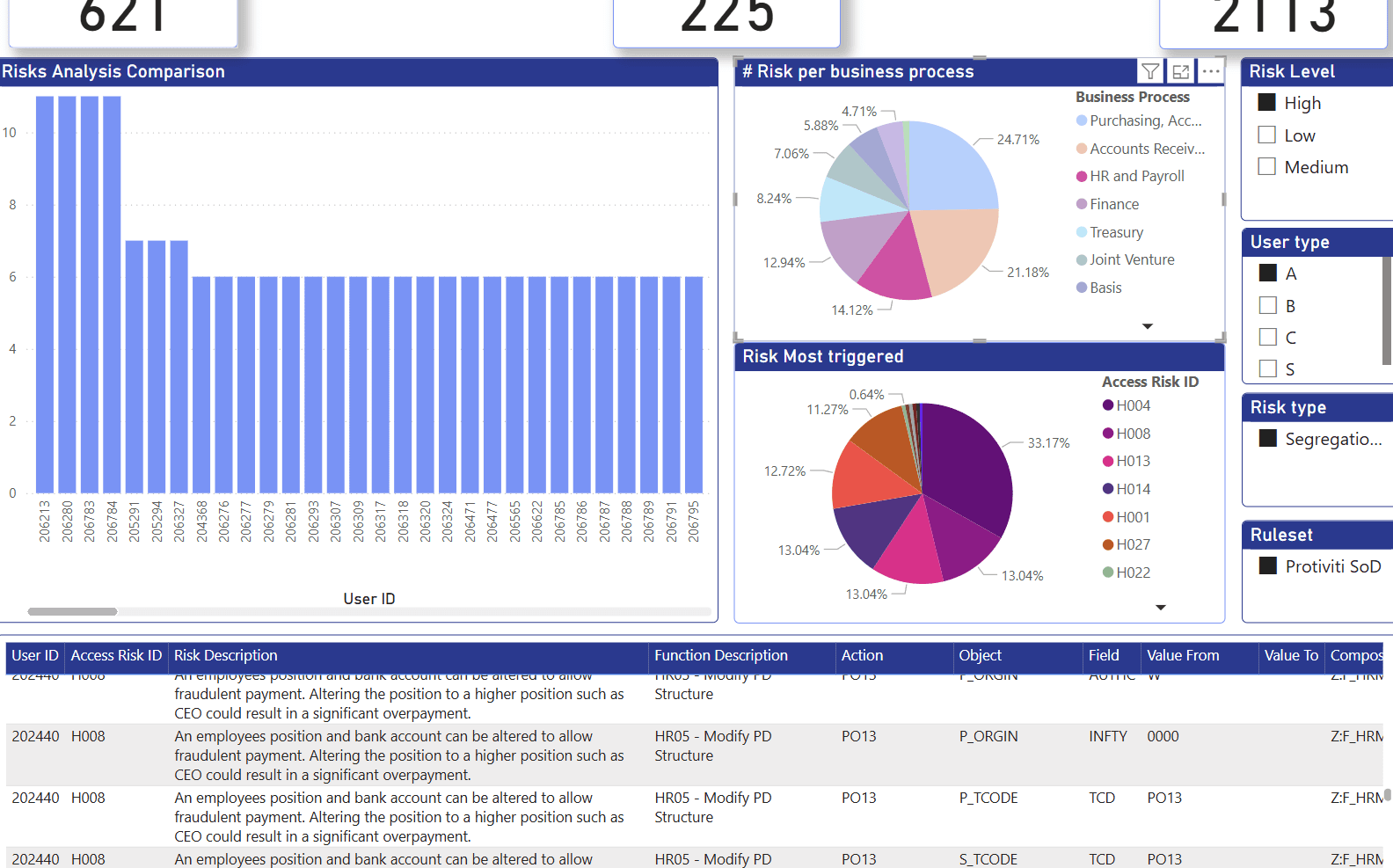
A practical guide to SAP authorization design that holds up in production. Covers role architecture, naming conventions, organizational value strategy, least privilege enforcement, critical access monitoring, and the change governance process that keeps your landscape clean over time.
Blog Posts
2026-03-05
2025-11-28
2025-08-05