Authorization-Level vs Transaction-Level Access Risk Analysis: Why Depth of Analysis Changes Everything
Transaction-level access risk analysis flags any user with access to two conflicting transactions. Authorization-level access risk analysis checks whether the underlying authorization values actually overlap, so conflicts that share no company code, plant, or organizational unit are filtered out as false positives. The distinction is not academic: on a real SAP landscape with multiple company codes, authorization-level analysis typically produces 3 to 10 times fewer conflicts than transaction-level, while catching the same real findings.
If your access risk analysis returns a conflict count that alarms the board but nobody can act on, the problem is usually the depth of analysis. This guide explains the difference and why it determines whether an access risk program is taken seriously or quietly ignored.
The core difference in one example
Take a classic SoD pair: create vendor master (XK01) combined with payment run (F110). A user who can do both is the textbook fraud case: invent a vendor, pay them, pocket the money.
Now add organizational scope. The user is authorized to:
- XK01 scoped to company code 1000 (Germany)
- F110 scoped to company code 2000 (United States)
What transaction-level analysis reports
Conflict found. User can create vendors and run payments.
What authorization-level analysis reports
No conflict. The user can create vendors in CC 1000 but can only pay in CC 2000. The authorization values do not intersect. No company code exists in which the user can execute both sides of the conflict.
Both analyses saw the same user and the same two transactions. They reached opposite conclusions. In a landscape with 10 company codes and 2,000 users, this disagreement scales into thousands of phantom conflicts that remediation teams cannot act on.
Why transaction-level analysis over-reports
Transaction-level tools take a shortcut: check whether the user holds access to tcodes on a conflict list. It is fast and easy to implement, and it ignores three things SAP's authorization concept cares deeply about:
- Authorization object fields. XK01 checks
F_LFA1_BUK(company code for vendor master). Without overlap onBUKRSfield values, there is no real path to execute both sides. - Organizational levels.
BUKRS,WERKS,VKORG,KOKRSall scope access. A tool that ignores them assumes the worst case for every user. - Activity values.
ACTVT = 03(display) is notACTVT = 01(create). A user with display-only on one side of a conflict cannot modify data, so they cannot realize the conflict.
Every SAP authorization is defined by (tcode, authorization object, field, value). Analysis that stops at the tcode level ignores three of the four dimensions.
Why this matters for the access risk report
The practical consequence of transaction-level over-reporting:
| Impact | Transaction-level | Authorization-level |
|---|---|---|
| Conflict count | Inflated (often 3-10x) | Realistic |
| False-positive rate | 60-80% in cross-org landscapes | Near zero |
| Remediation team credibility | Erodes over time (too many "conflicts" are non-issues) | High (each finding is actionable) |
| Audit defensibility | Auditors must re-verify every finding | Auditors accept findings as real |
| SoD remediation velocity | Slow (analysts debate which are real) | Fast (act on every finding) |
The secondary effect is cultural. Remediation teams that spend 80% of their time dismissing false positives stop taking the access risk analysis seriously. The tool becomes a compliance checkbox, not a security function.
Where each approach makes sense
Transaction-level analysis is not wrong in every case:
- Small, single-company-code environments where every user's scope is effectively
*. Both analyses converge. - Initial ruleset validation. A fast transaction-level pass can identify gaps in the ruleset before running a full authorization-level scan.
- Vendor sales demos. Transaction-level counts produce impressive (scary) numbers that sell the tool.
Authorization-level analysis is needed in:
- Multi-company-code landscapes, which covers any organization above mid-market.
- Multi-plant or multi-profit-center environments (manufacturing, retail, utilities).
- Organizations with derived role architectures where organizational fields are the entire scoping mechanism.
- Any environment where the access risk report has to survive an external audit.
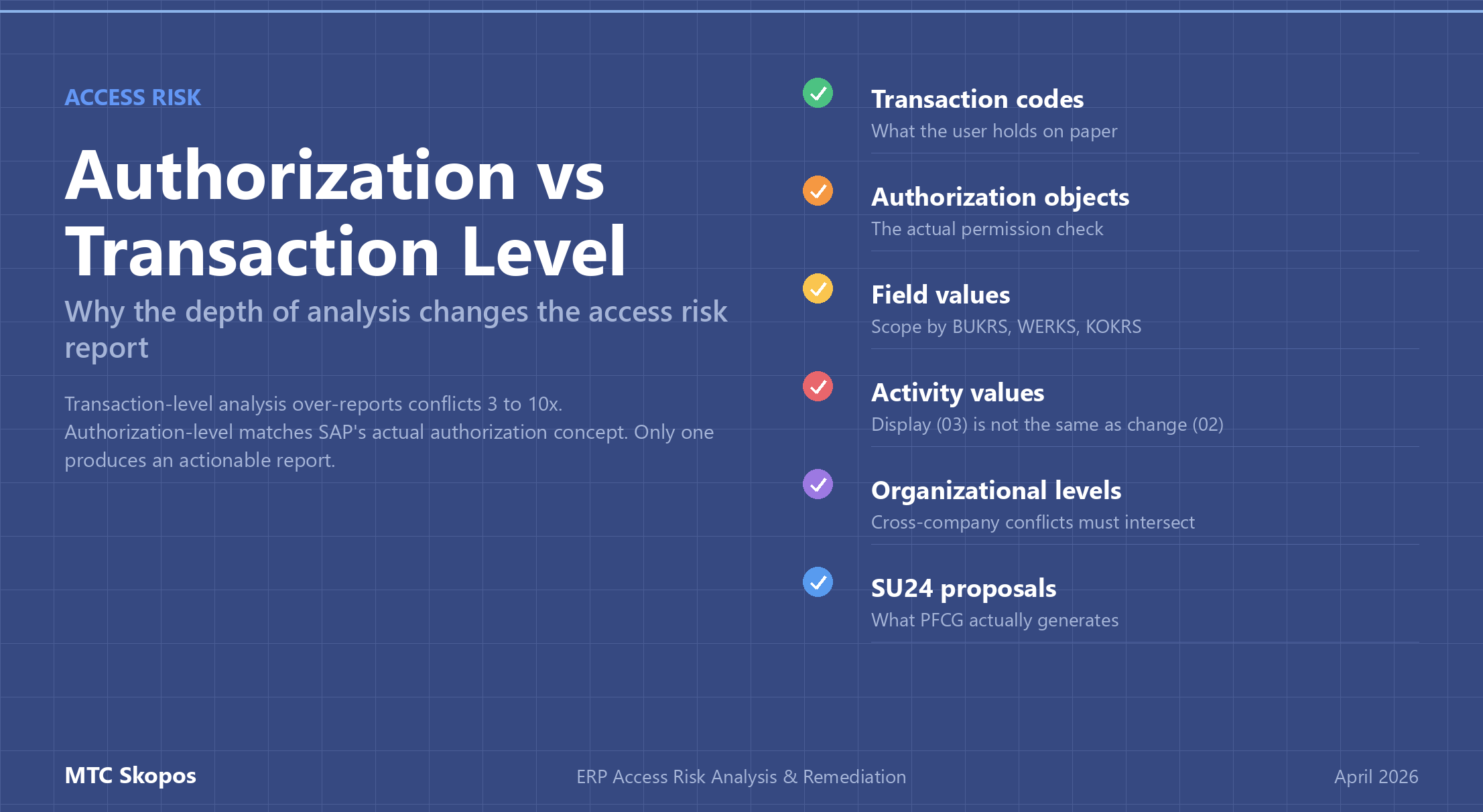
What authorization-level analysis actually checks
For every SoD conflict pair, authorization-level analysis evaluates the intersection across multiple dimensions:
- Transaction codes. The user must have both tcodes in the conflict.
- Authorization objects. The user must have the relevant authorization objects on both sides (e.g.,
F_LFA1_BUKfor vendor creation,F_REGU_BUKfor payment). - Field values. Specific authorization fields must have overlapping allowed values (e.g., same
BUKRSvalues on both sides). - Activity values. Both sides must permit the activity that makes the conflict real (typically
ACTVT = 01create or02change, not03display). - Organizational levels.
BUKRS,WERKS,BUDAT,KOKRS, and any others relevant to the conflict. The scope has to intersect. - SU24 proposals. The analysis has to reflect what PFCG actually generates from SU24, not a theoretical mapping.
Miss any one of these and the analysis degrades toward transaction-level accuracy. That is why SU24 maintenance is fundamental: accurate authorization-level analysis depends on accurate SU24 data.
How MTC Skopos handles this
Authorization-level analysis is the default mode in MTC Skopos. The tool reads the full authorization chain (transaction, authorization object, field, value, organizational level) and evaluates SoD pairs as set intersections on the actual values. No intersection, no conflict reported.
This is paired with:
- Did-do analysis, which separates theoretical from actually-exercised conflicts
- Critical access detection, which runs in the same pass with authorization-value precision, so critical access findings are not over-reported either
- Cross-company-code scope verification, with organizational fields treated as first-class inputs rather than approximations
Teams moving from a transaction-level tool to authorization-level analysis usually see a dramatic drop in reported conflict count. The real conflicts did not disappear; the false-positive layer did. What remains is actionable.