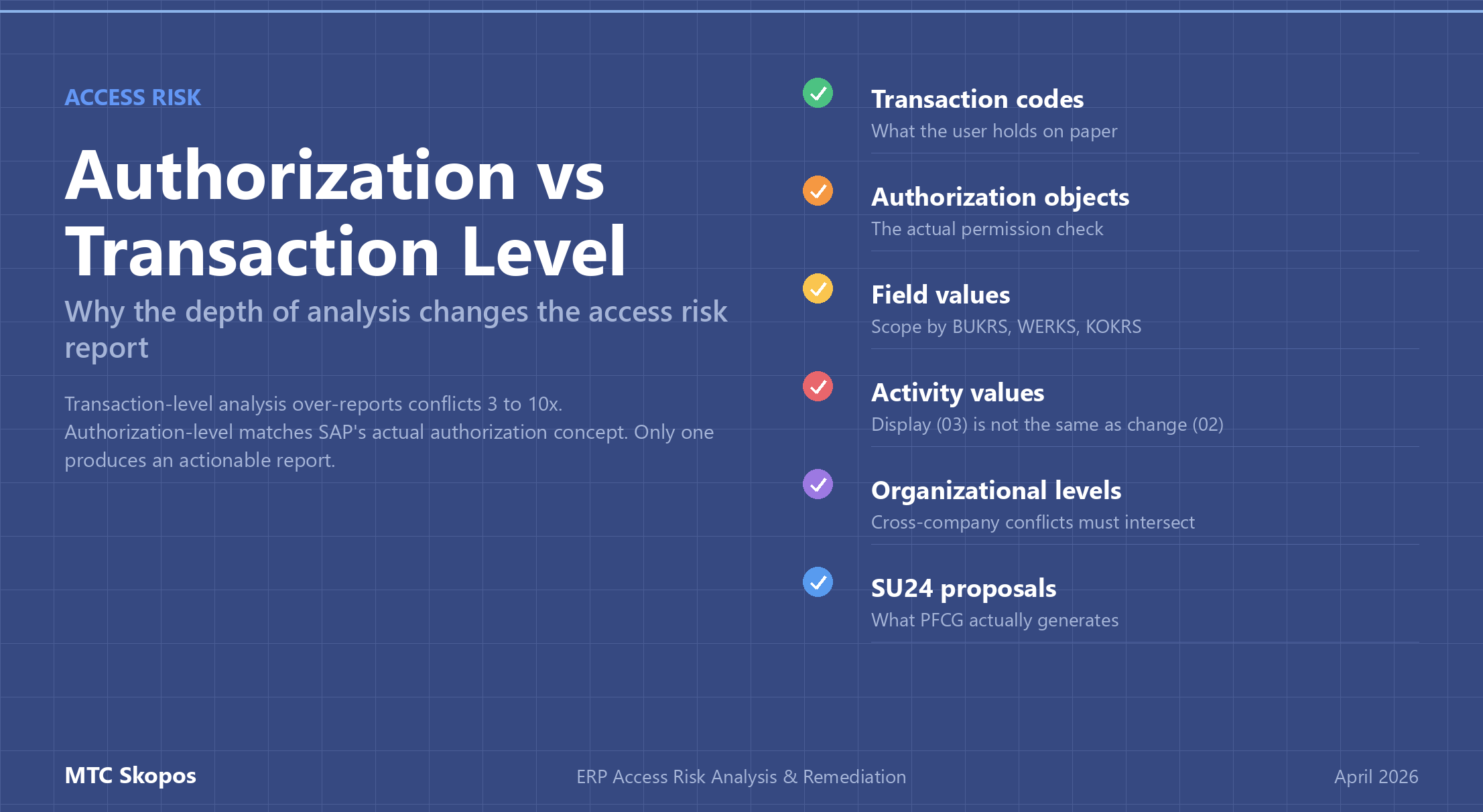
Most access risk tools analyze SoD at the transaction code level: if a user has tcode A and tcode B, flag a conflict. Authorization-level analysis goes deeper. It checks whether the user's authorization object values actually overlap, so conflicts that share no company code, plant, or organizational unit are filtered out. The distinction matters: transaction-level analysis on a large SAP landscape typically produces 3-10x more false positives than authorization-level analysis.
SAP Authorization: Articles & Insights
Technical SAP authorization topics: role design, critical access, SoD rulesets, S/4HANA specifics, and authorization best practices.
Found 8 articles in this category.
All Articles in "SAP Authorization"
Want to learn more about ERP access risk management? Explore MTC Skopos features for comprehensive Segregation of Duties analysis and remediation.
MTC Skopos © 2026